What Is Search.exploremethod.com Mac Virus?


Apple is going to make it even harder for malware like Search.exploremethod.com to take over users’ Macs, with a new Safari feature that blocks unwanted software from being installed on the computer. However, somehow this browser hijacker still manages to infiltrate some older Mac versions. Search.exploremethod.com is classified as a browser hijacker and is installed on the system via various methods. The most common way this malware manages to infiltrate the system, aside from bundling with free software on the Internet, places it on a user’s Mac by exploiting vulnerabilities in web browsers that allow it to attach itself to websites visited by unsuspecting victims. Once attached, however, it changes the extension of several popular webpages and alters their characteristics in order to make them look more trustworthy and force users into downloading it.
How Is Search.exploremethod.com Mac Virus Distributed?
As a browser hijacker, Search.exploremethod.com virus usually enters the system using various methods, which means that each time you’ll see this browser hijacker on your computer, it will be because of some different reasons. In the majority of cases , this threat is distributed through bundled downloads . Some third party software are known to spread malware between users in order to make more money from their software and from advertisements shown on their search engines. Other ways this browser hijacker is spread include spam email attachments, fake free software updates and gaining access to a user’s personal files through hacking accounts on specific websites.
How harmful is Search.exploremethod.com hijacker?
As you might have already realized, this browser hijacker is generally unwanted software that affects the browsing experience of users in a negative way. Generally, it is not considered to be a malicious threat and won’t take any action that might put your Mac at risk. However, because of how this adware works, many security experts state that it is best to remove Search.exploremethod.com as soon as you notice its presence on your Mac. This browser hijacker might be dangerous for a number of reasons and it is best to remove this threat from the system as soon as possible.
How did I get infected?
This hijacker is not something that you can install from the official Mac App Store. Instead, it can be brought in to the system by bundled software such as free trials for new software or self-extracting archives. Since this browser hijacker has been classified as a potentially unwanted application, users should never install software or executables from unfamiliar sources. The most efficient way to remove this browser hijacker from your Mac is by using a legitimate anti-malware scanner. Most malware removal applications will show signs and symptoms of Search.exploremethod.com hijack, and this should be enough to allow you to identify the threat on your own.
How can I remove Search.exploremethod.com virus ?
Step 1: Uninstall Search.exploremethod.com and remove related files and objects
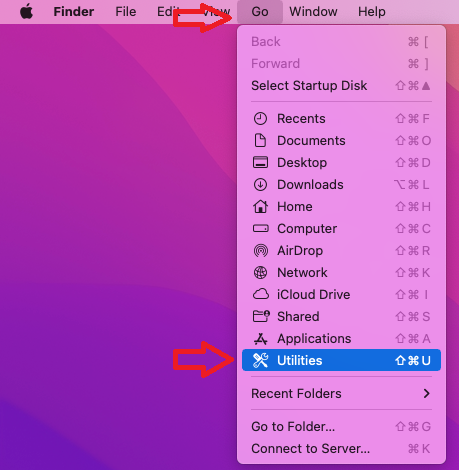
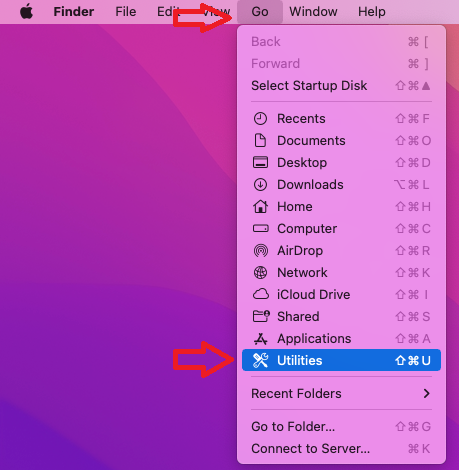
- Open your Finder –> Click on GO –>Click on Utilities
- Find Activity Monitor and open it
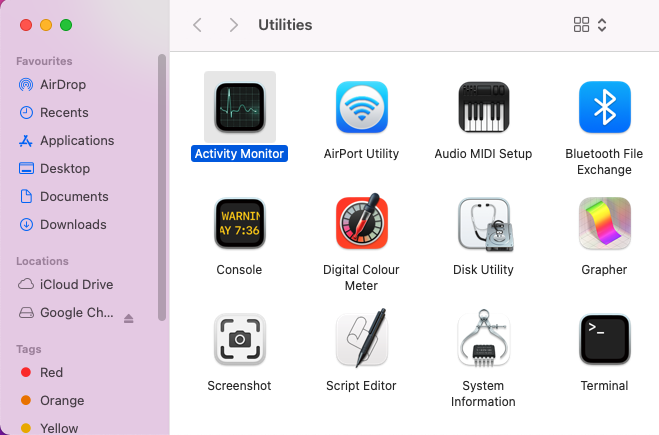
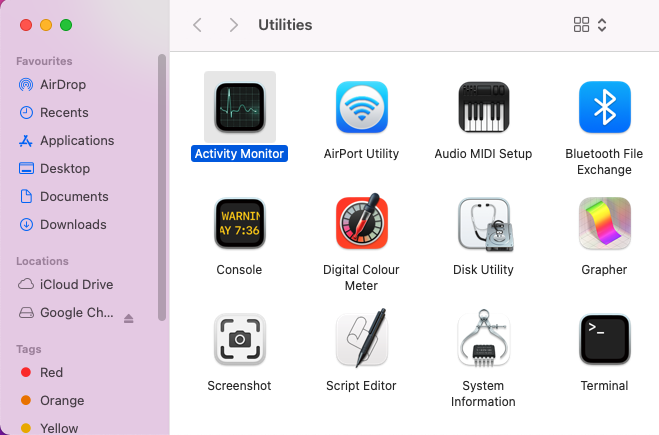
- Review all the processes in Activity Monitor and write down the ones related to Search.exploremethod.com virus
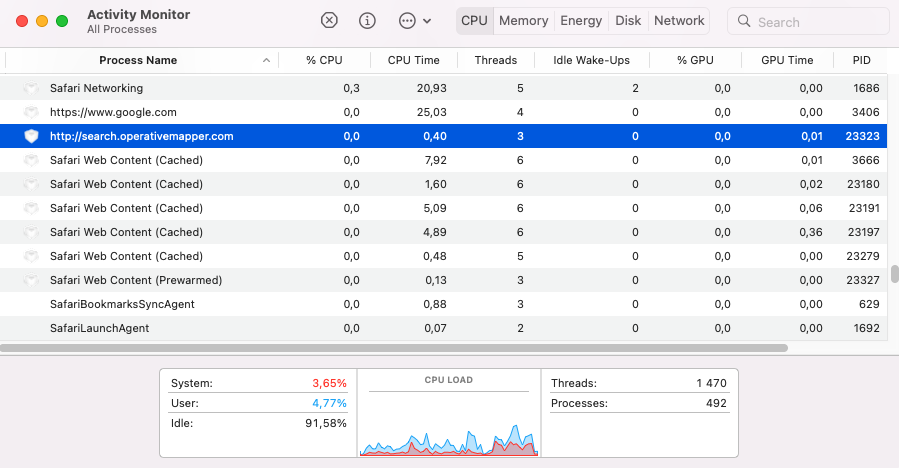
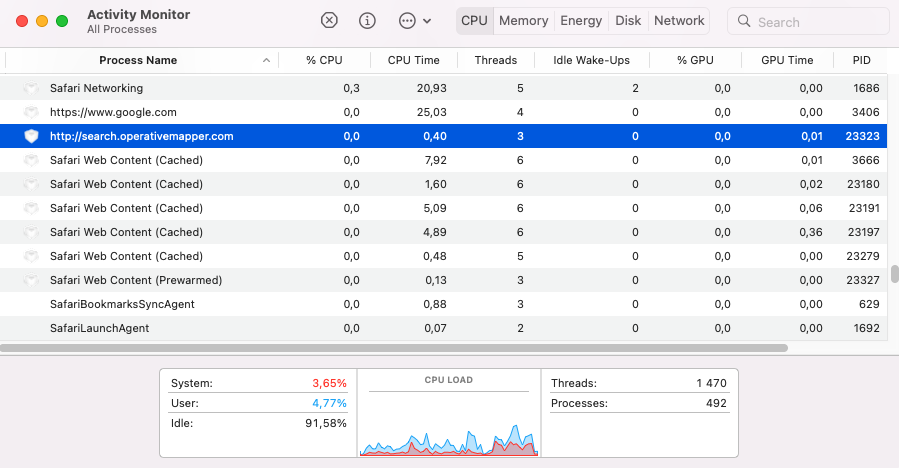
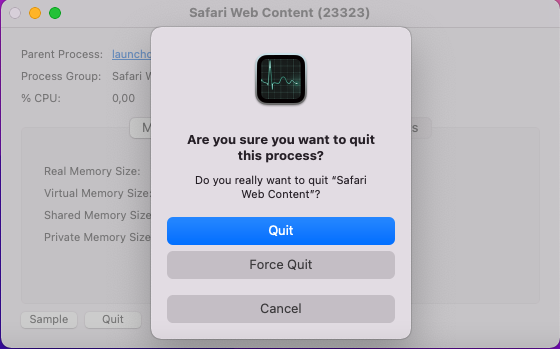
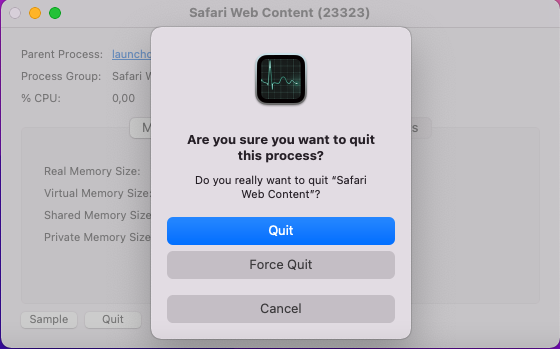
- Select Quit
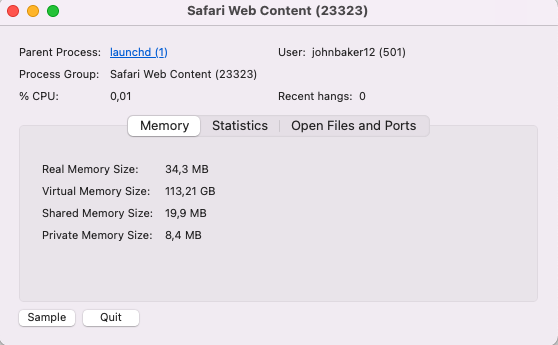
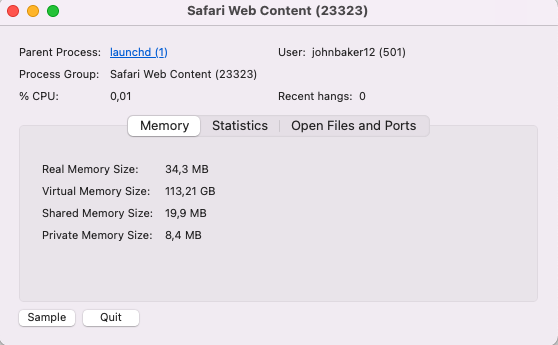
- To kill the malicious process, choose the Force Quit option.
Step 2: Remove Search.exploremethod.com – related extensions from Safari / Chrome / Firefox
The first thing you need to do is to make sure Safari is not running. If you have troubles closing it, you may need to Force Quit Safari - (Start Activity Monitor by opening up Finder, then proceed to Application --> Utilities --> Activity monitor. Locate the Safari process and force quit it.
Safely launch Safari again by holding the Shift key and clicking on the Safari application icon - This will prevent Safari’s previously opened malicious web pages.
In case that you still are having trouble with scripts interrupting the closing of unwanted pages, please do the following:
- Force Quit Safari again.
- Disconnect form Internet and try again.
Then Re-Launch Safari but don’t forget to press and hold the Shift button to prevent pop-ups. Then, click on Preferences.
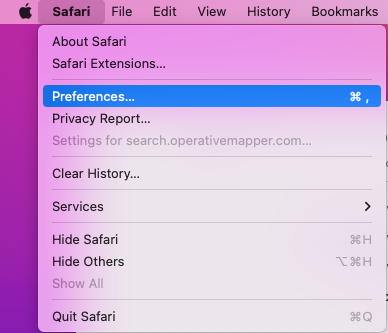
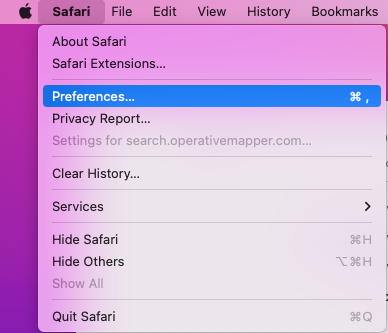
- Carefully take a look at your default home page and change it if the hijacker altered it.
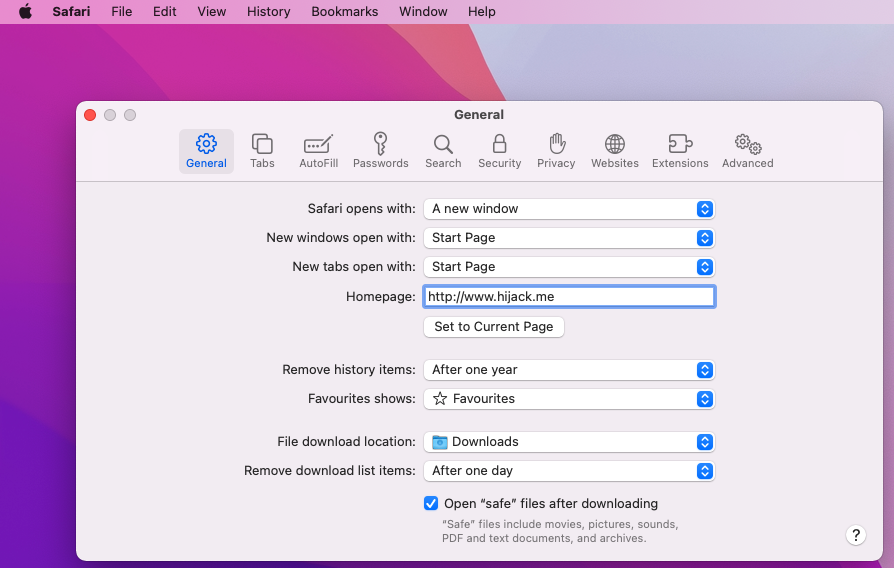
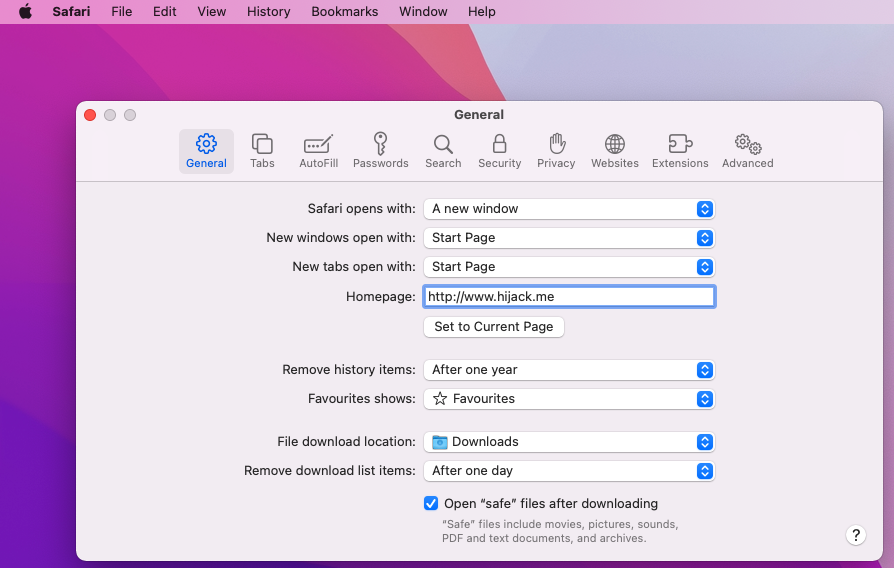
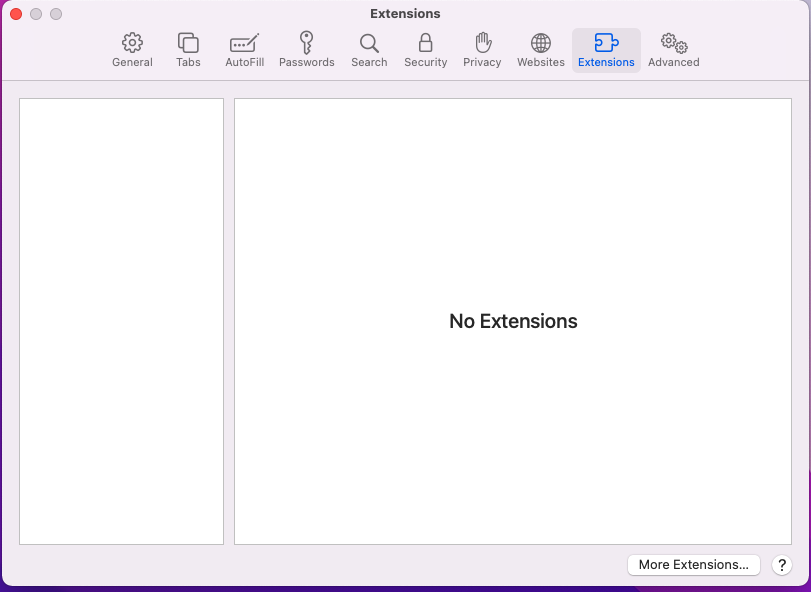
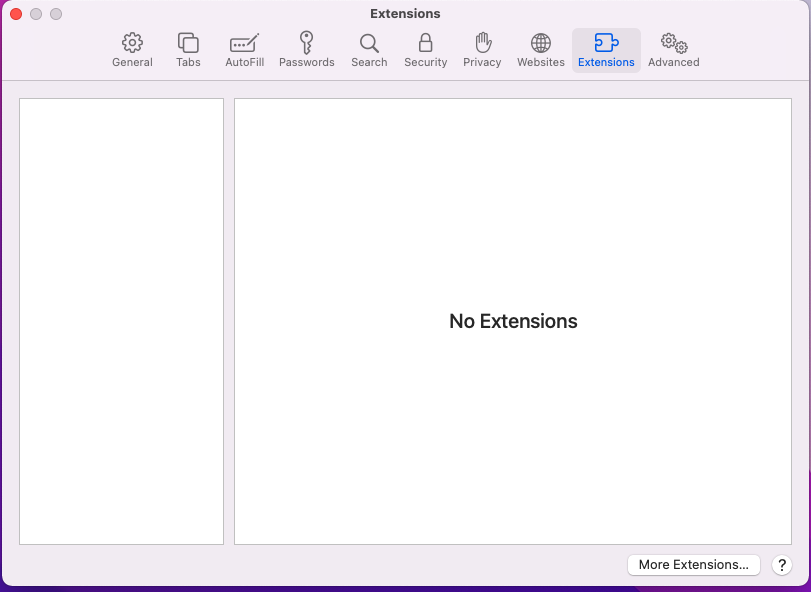
- Then go to the Extensions tab and make sure there are no unknow extensions installed.
- Next step is to click on Privacy tab
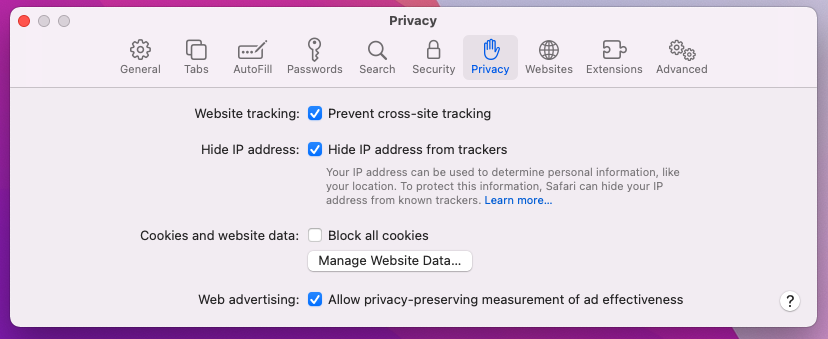
- Manage website data
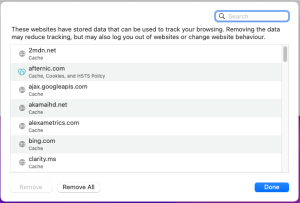
- Here you can remove any unwanted website data or just remove them all. Please, keep in mind that after you do this all stored website data will be deleted. You will need to sign-in again for all websites that require any form of authentication.
- The next step is to Clear History (if you want), select the tab.
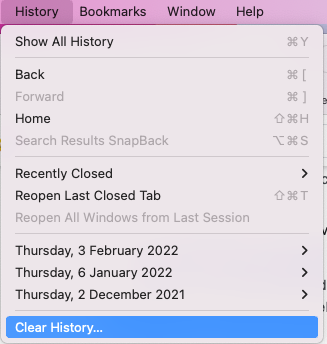
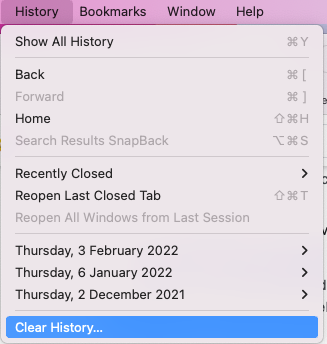
- Click the menu next to clear and choose a time period — if you want to completely reset Safari, choose all history.
- Press Clear History
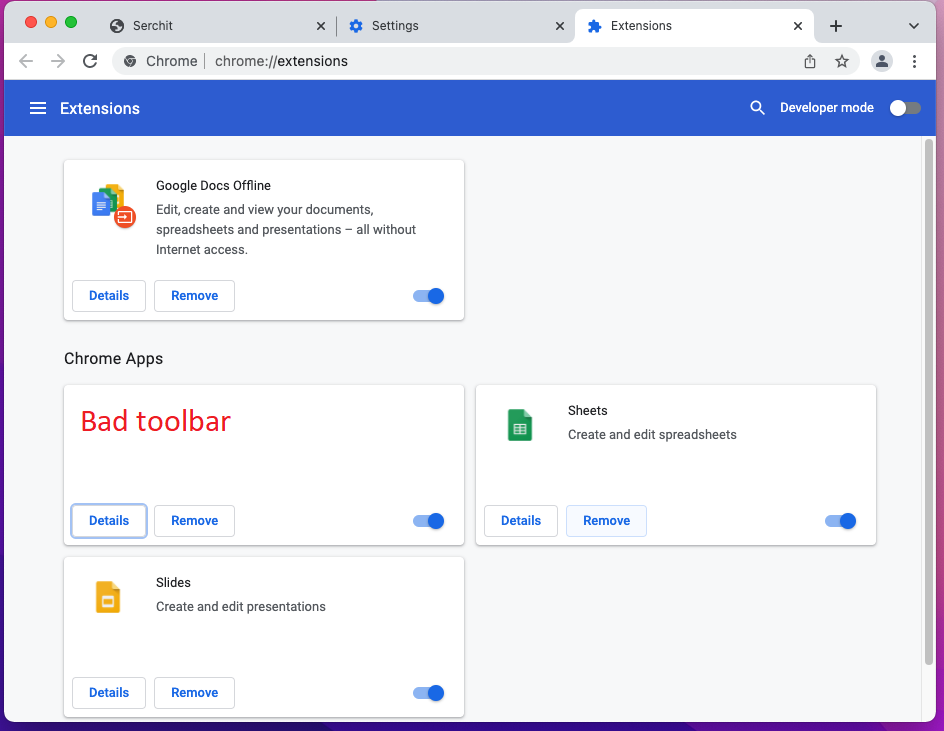
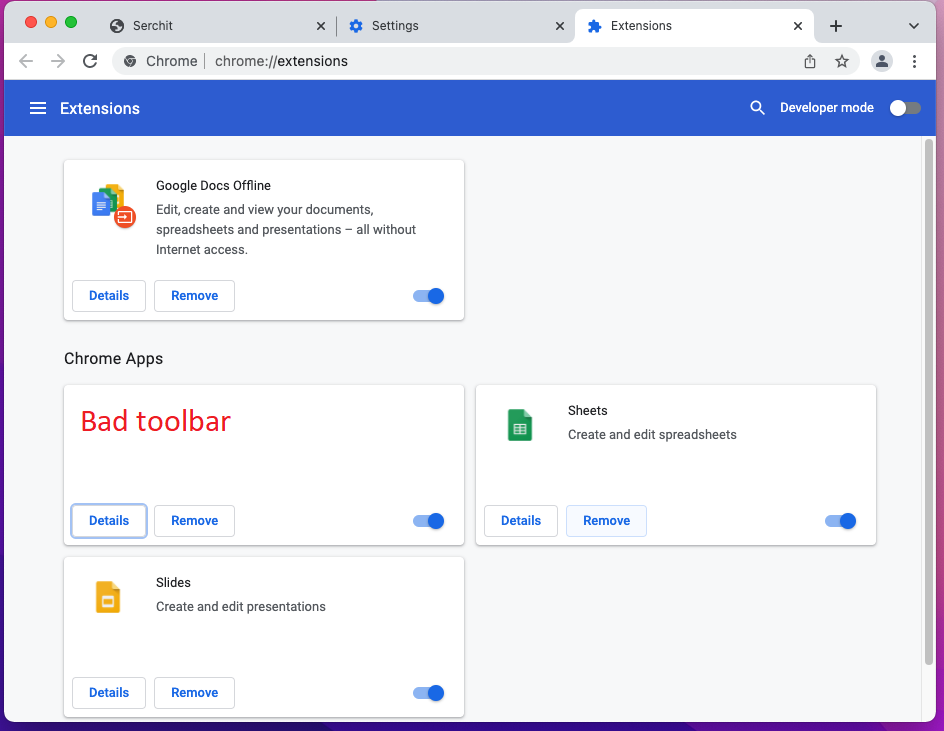
- To remove from Chrome, open the browser and click the icon with the three dots located in the top-right.
- Select to More Tools --> Extensions and review what Chrome Extensions are present in the browser


- Remove the ones that you do not recognize.
- If the parasite continues to disrupt your browsing with Chrome, this is what else you can do:
- Click again the menu of Google Chrome, and open Settings.
- Select the Search Engine from the left panel, review the available search engines and change the default to your preference.


- Then, click on Manage Search Engines, review the list of search engine availabilities and if any of the listed items looks suspicious, click the three-dots next to them, and delete.


- Click on Privacy and Security in the left panel, select the Clear browsing data option, check every box except the Passwords one, and click Clear Data.


- Next step is to clear Notifications, select the Site settings option in the Privacy and Security section, then locate Notifications.


- Review the listed websites in the Allow to send notifications section and if any of the entries shown there seem dubious or related to the browser hijacker, select the three dots next to the object and click on Remove.
- Start Mozilla Firefox
- On the top right click the three dashes
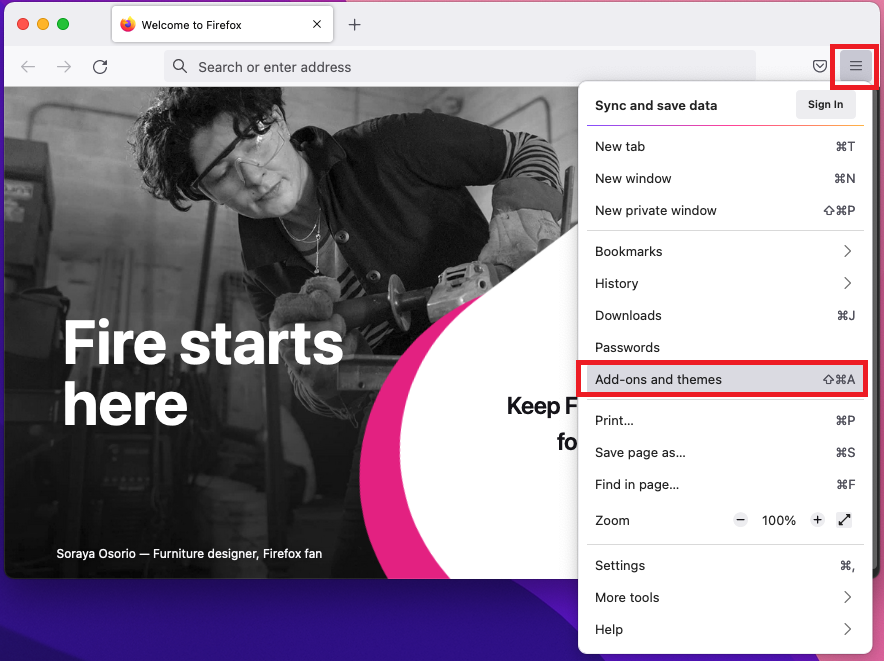
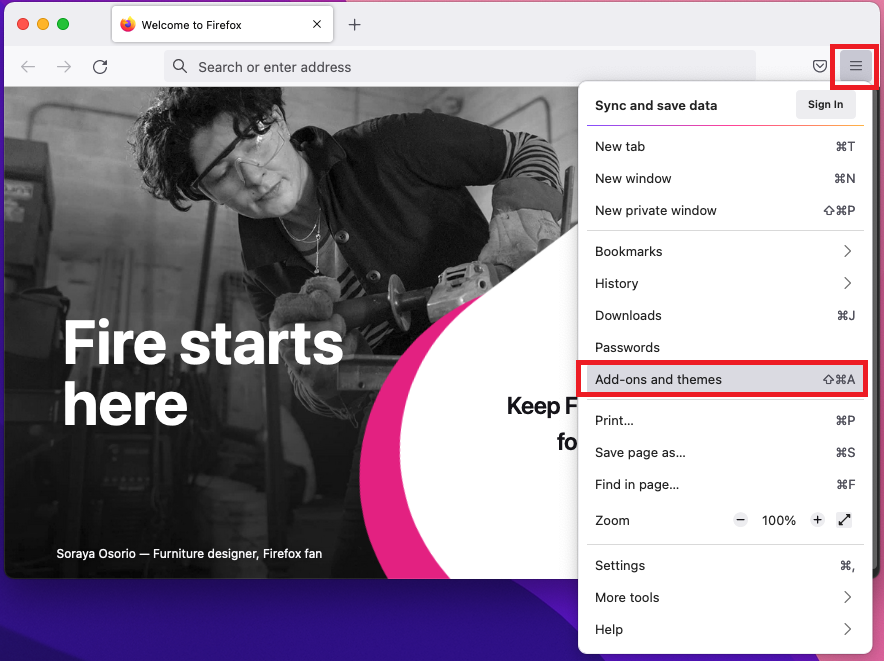
- go to add-ons and themes
- The add-ons manager will open
- Carefully review review four Firefox Extensions
- If any unwanted extension is present, click on the three horizontal dots and then Remove
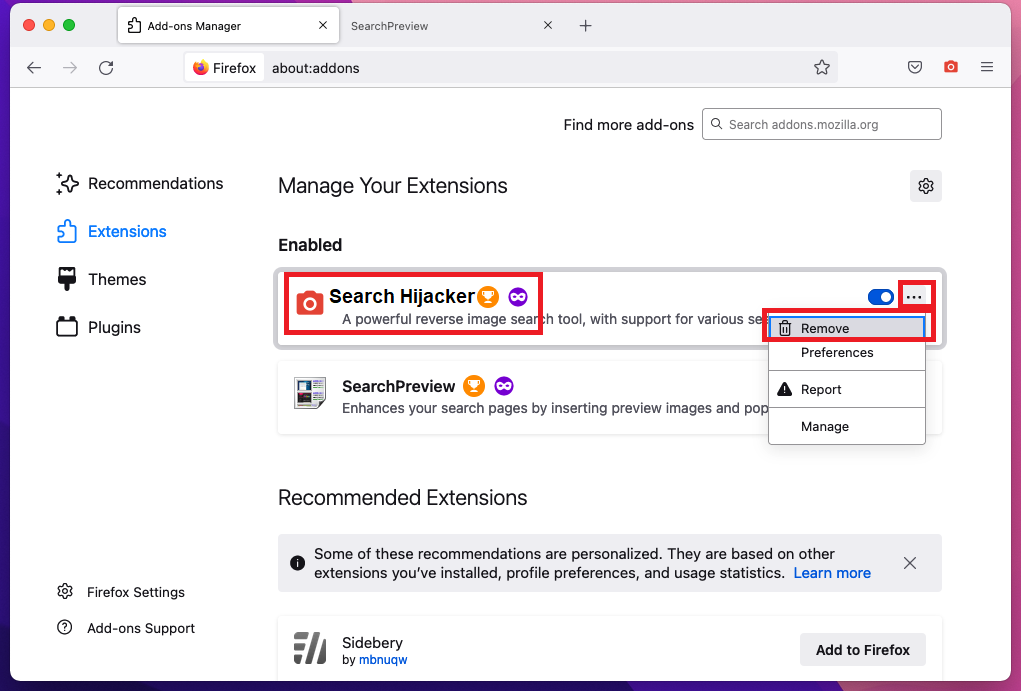
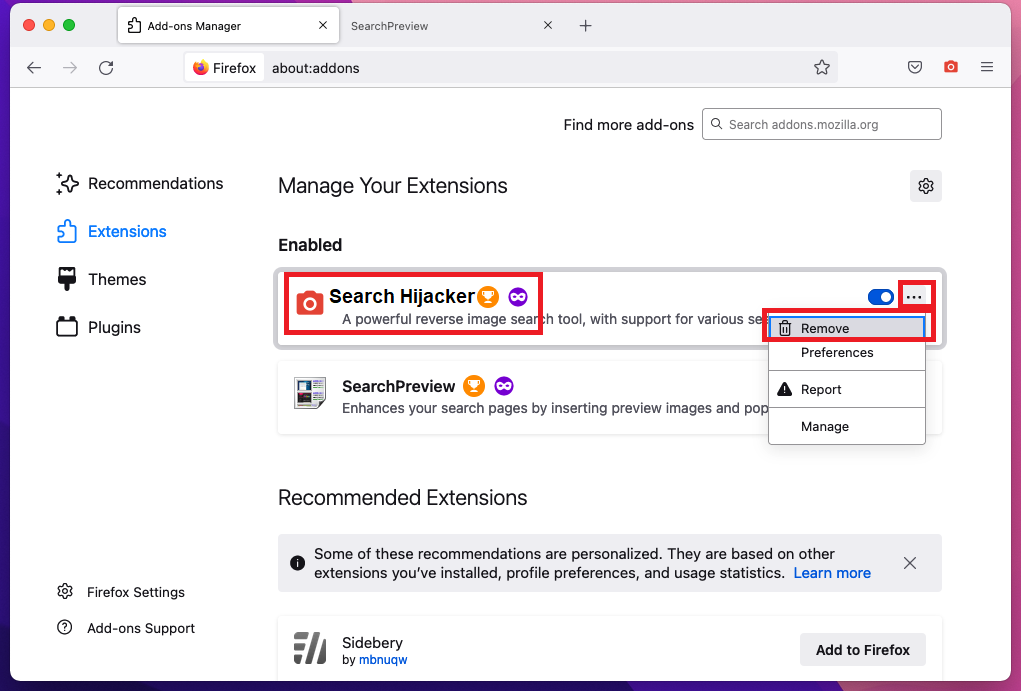
- After the extension is removed, restart Mozilla Firefox by closing it from the red dot in the top left and start it again.
Step 3: Scan for and remove Search.exploremethod.com files from your Mac
Fix your browser settings with SpyHunter Anti-Malware
Once you download and install SpyHunter for Mac run a scan.
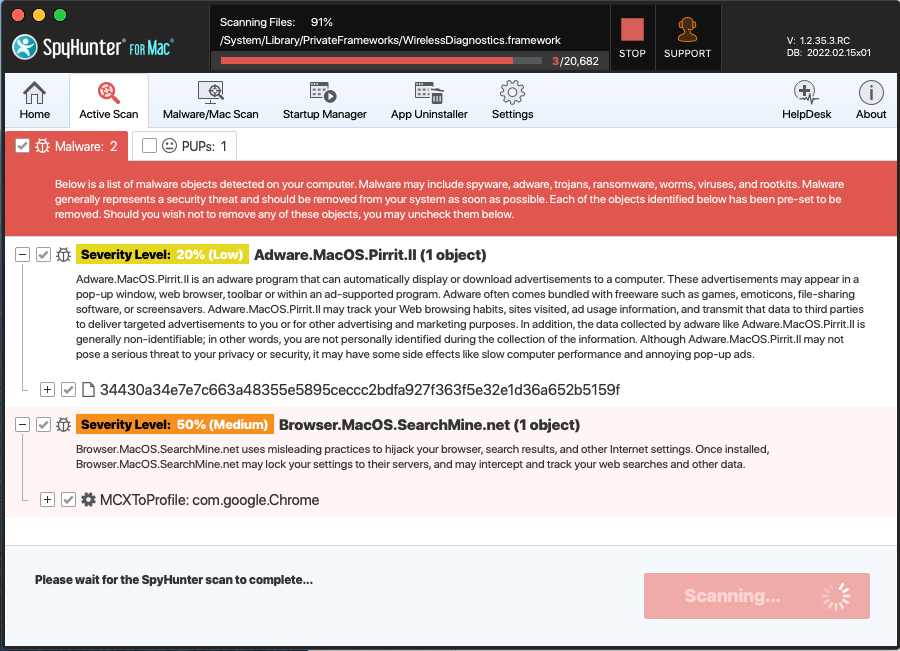
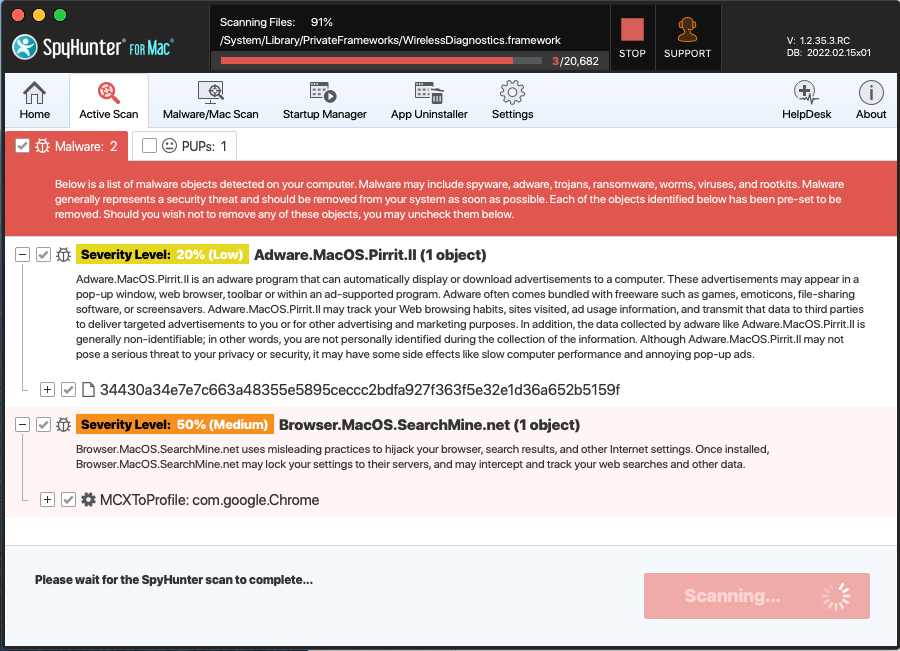
Once the scan is complete, your mac will be virus free.
Search.exploremethod.com malware Frequently Asked Questions:
- How do I get rid of Search.exploremethod.com?
Search.exploremethod.com is a Browser hijacker – malicious software that can be installed by third-party applications or websites. They usually change the settings of web browsers and search engines to display certain ads, pop-ups, banners, etc.
- What are the symptoms of Search.exploremethod.com infection in your Mac?
Search.exploremethod.com becomes your web browser’s built-in search engine.
Your browser’ s search queries are redirected through Search.exploremethod.com.com
The “Search.exploremethod.com” browser extension or some shady software is installed on your Mac.
- How do I remove Search.exploremethod.com from my browser?
In Internet Explorer, click the gear icon on the top left and select Manage add-ons. Under Add-on Types, select Search Providers. Select your search engine from the list of providers and click Remove to remove it. In Google Chrome, go to Settings (at the top right) and choose Search in the On Startup drop down menu.
- How do I uninstall Search.exploremethod.com?
How to Make Your Mac Run Faster?
You might be wondering how to make your Mac run faster? It is a common misconception that the more processing power you have, the faster your computer will run. In reality, it’s actually about what’s going on in your processor and memory. For the average person using a computer for just general applications like word processing and web browsing, you don’t need much in the way of computing power.
– Use an SSD drive instead of a hard disk drive.
– Double your RAM if possible.
– Disable System Integrity Protection (SIP). (Attention! – do this only if you know the consequences.)
References:
- More about pop-up advertisements on Wikipedia.
- MacOS malware
- SpyHunter Anti-Malware overview and also the reasons why we recommend it for malware elimination.
Please, have in mind that SpyHunter offers a free 15-day Trial version with full functionality. Credit card is required, no charge upfront.

